⚠️ CRITICAL BUG: Do NOT Play on Public PCs - Arknights Endfield Account Hijacking Risk
news
urgent
security
bug
warning
Major security flaw found in Arknights Endfield PC client. Login cache files (mmkv) lack device verification, allowing hackers to steal your account easily. Learn how to protect yourself.
⚠️ CRITICAL SECURITY WARNING: PC Client Vulnerability
Do NOT log in to Arknights: Endfield on any computer that is not your own personal desktop.
Currently, Gryphline has not implemented any device verification for login cache files. This means that the login session is not bound to your hardware.
The Vulnerability: Session Hijacking
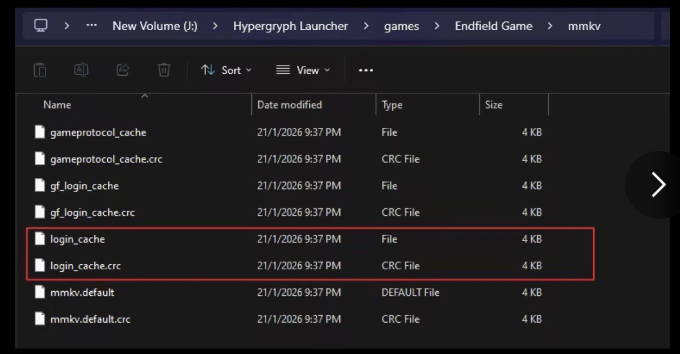
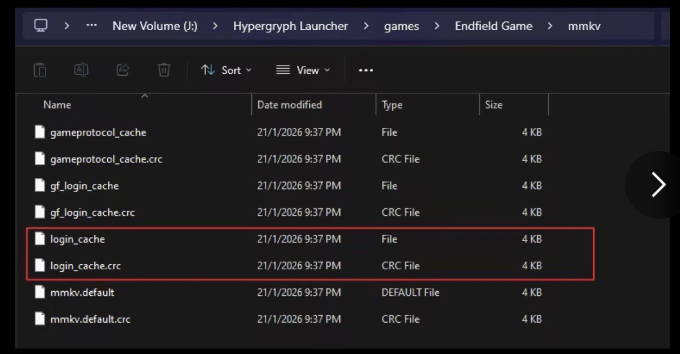
As shown in the screenshot below, the game stores your login session in the mmkv folder.
How it works:
- No Encryption: The
login_cacheandlogin_cache.crcfiles are not encrypted or bound to the PC. - Remote Hijacking: If someone copies these two files from the computer you used, they can paste them into their own game folder.
- Direct Access: They can then bypass the login screen and remotely log in to your account directly, without needing your password or 2FA.
High-Risk Scenarios
- Internet Cafes / Cyber Cafes: If you play on a public PC, the next user can easily steal these files.
- Shared Computers: Playing on a university or library computer.
- Malware: Stealer trojans can easily target these specific files to hijack high-level accounts.
How to Protect Yourself
Until Gryphline patches this vulnerability (adding Hardware ID verification to the cache), you must take these precautions:
- Play ONLY on Personal Devices: Do not log in on any computer you do not fully own and trust.
- Manually Clear Cache (If you used a public PC):
- Navigate to the game directory:
.../Endfield Game/mmkv/ - DELETE all files in this folder before logging out/leaving the computer.
- Just clicking "Logout" in-game might not be enough if the files were already copied.
- Navigate to the game directory:
- Enable 2FA: While this exploit bypasses the initial login, having 2-Factor Authentication enabled on your Gryphline account is still a crucial layer of defense for account settings changes.
Summary
This is a "Session Hijacking" vulnerability. It is extremely easy to exploit. Please spread the word to your fellow Administrators to prevent account theft.
Stay vigilant. We will update this post once an official patch is released.